The term “Web3” usually refers to the blockchain, cryptocurrencies, and NFTs. However, in reality, it describes a new version of the internet in which identical data is stored and accessed through a network of numerous servers.
Now, more than ever, regular practice is essential for safe browsing habits on the internet as corporations, organizations, governments, and individuals all begin upgrading to the more secure Web 3.0.
Web 3.0 is still evolving and is not yet mature enough to provide a genuinely immersive metaverse experience.
Several dangers come side by side with these innovations. An in-depth analysis of the new security risks that users face and producing a set of best practices to assist them is essential knowledge for these users to acquire.
Not to worry, we understand that new security risks come along with these opportunities. We also have put together safety measures and instructions to enable users to stay safe online while exploring the benefits of Web 3.0.
To this effect, this article has compiled top recommendations for Web 3.0 security.
Outline
- Why Web3?
- Examples of Web3 applications
- Security Issues in Web3
- Five ways to play safe
- Conclusion
Why Web3
The goal of Web3 is to undermine the market dominance of these centralized entities by replacing the server-client infrastructure with distributed ledgers, the most popular of which is the blockchain. As a result, data won’t be kept on a single server but rather dispersed over a decentralized computer network. Thus, centralized organizations that served as past intermediaries will become extinct.
Here’s an illustration of Web 2 banking. Today, everyone transmitting money between banks uses the centralized servers provided by various banking companies. Banks carry out these transactions by serving as mediators. Therefore, the user must provide all the necessary information to the participating banks and rely on them to complete the transaction correctly.
Of course, the bank makes a profit from this service. In Web3, you can make transactions utilizing a decentralized blockchain like the Bitcoin blockchain. This blockchain independently confirms the transaction’s accuracy through mathematics and processing power.
Banks are no longer necessary as intermediates, unlike Web2. This fact implies that the user maintains sovereignty over their data and that no fees are required because no centralized entity is profiting from the transaction.
Hence, Web3 is meant to give users back control over their data and ownership rights. To learn the basics of Web3, click here.
Examples Of Web3 Applications
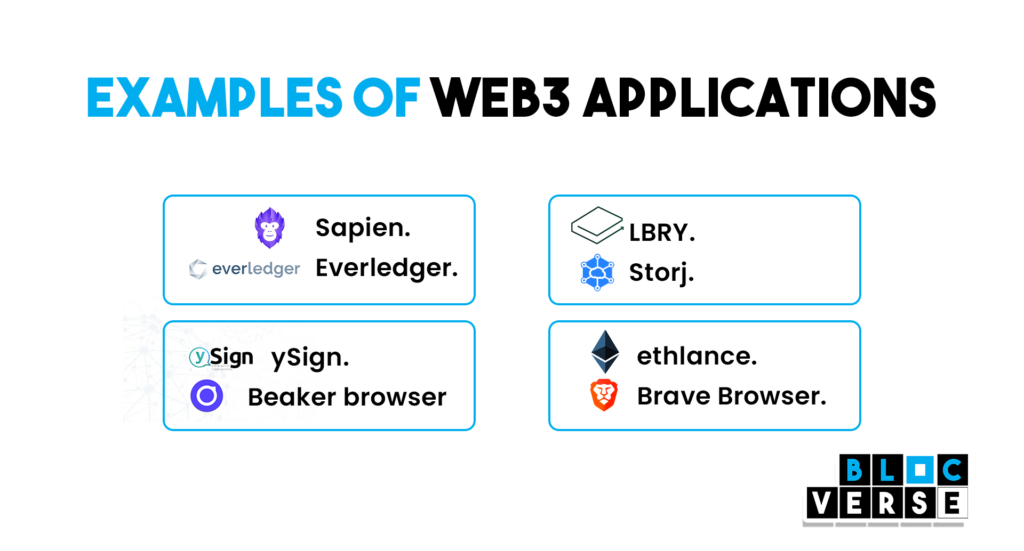
The decentralized cryptocurrency functions as a peer-to-peer network based on blockchain technology and does not require banks or central banks. The Ethereum blockchain was created using the same technology as the Bitcoin blockchain, which was introduced five years earlier. The Ethereum Blockchain and other blockchains are currently home to a wide range of applications.
Using smart contracts, Ethereum enables the automation of token-based transactions. These include decentralized financial apps (Defi) like Crypto Lending, where savers use a Defi platform to generate liquidity for loans and profit from the process through interest.
For creating a “trustless” network, smart contracts take the role of centralized middlemen like banks. As a result, the value chain is made cheaper and more effective by eliminating intermediaries. Another Web3 application is NFTs (non-fungible tokens). NFTs represent securitized ownership of a digital asset that you can use to identify it specifically, such as a graphic, piece of art, or domain.
Due to their unique characteristics, NFTs make it possible for digital property rights to be transparently documented and transferred automatically without centralized intermediaries.
Other Web3 applications include:
- Sapien.
- Everledger.
- LBRY.
- Storj.
- ethlance.
- Brave Browser.
- ySign.
- Beaker browser
Setbacks In Web3 – Security Issues in Web3

Web3 is still in its infancy; hence, there are many questions. Like Web1, where technical scalability was a problem, decentralized networks process data far more slowly than centralized Web2 networks. For instance, transactions over the Bitcoin network happen far more slowly than those over the Visa or Mastercard networks.
Web3 applications now fall behind Web2 applications in terms of user experience. For example, many customers find applying for a loan on a Web3 platform more challenging than on a Web2 fintech or bank. Web3’s degree of decentralization is another issue to consider. Web2 infrastructure continues to be necessary for Web3 to work, at least for the time being. Most Web3 applications would no longer be accessible if infrastructure providers like Amazon Web Services failed.
Venture capital firms also fund a lot of decentralized apps, and because they possess many tokens, they can influence the network’s decisions.
Two examples of this are:
- Uniswap – a cryptocurrency exchange.
- Compound Finance – a cryptocurrency lending technology.
Web 3.0 And User Privacy
Here are a few ways Web 3.0 and blockchain might help assure a privacy-driven future for individuals and eliminate some of the harmful influences currently exerted by corporations:
The use of blockchain technology
By default, a blockchain is a decentralized technology that prohibits any individual or organization from exercising total control over an ecosystem. Instead, all users can keep control collectively. In addition, a blockchain is a database that stores record while algorithmically maintaining their security and transparency, notwithstanding the absence of a single controlling organization.
Appropriate incentives within the ecosystem
All parties must operate honestly and transparently, from those who maintain the ledger and power the network to those who establish businesses on the blockchain. Those who do not comply can be penalized based on the blockchain’s rules or community voting. Users can and will continue to provide their data, but they will be aware of its precise application.
For example, with the effective implementation of blockchain, users will determine when, how, and how long their data is shared. Moreover, users must be aware of its precise application.
Users can withdraw data sharing at any moment.
Suppose users are uncomfortable with how their data is used or no longer wish to share data with a particular organization. In that case, they should be allowed to withdraw access to their data.
Less Hackable
Several precautions make it computationally hard to attack blockchain at this time. First, the widespread global adoption of Bitcoin demonstrates that blockchain is now unhackable. According to ITRC and the US Department of Health and Human Services, 98.2 million individuals have been affected by the ten most significant data breaches during the first half of 2021.
As the competition against hackers intensifies, blockchain technology provides additional security.
5 Ways To Play Safe With Web3

Many people are hesitant to engage in or participate in Web3 or blockchain technology because they have heard stories of hacks that terrify them. However, there are evil actors everywhere, and the only sure way to avoid them is to understand security fundamentals.
Users can significantly enhance their security by developing the practice of selecting solid passwords and utilizing multi-factor authentication when possible. In addition, by segmenting networks, monitoring network traffic, and analyzing these logs, organizations can identify issues before they become severe.
In addition, it is crucial to examine the Internet, ENS domain, and crypto wallet addresses for cleverly concealed typos indicative of fake websites.Therefore, people must not click on links delivered to them via social media or email without their consent.
Here are five ways you can play safe with Web3:
- Do not reveal your seed phrase to anyone.
Your wallet will generate a seed phrase, also known as a recovery phrase, granting you complete access to all your assets. It consists of 12–24 random words. There is zero chance that you will ever be obliged to reveal it because it gives you full access. Keep a physical copy of your seed phrase at all times; do not save it in internet storage or cloud services
- Research Independently
There’s a reason “DYOR” (do your research) is a catchphrase in the crypto sphere. Scams, rug pulls, and FOMO (fear of missing out) propagated by influencers or major accounts have claimed the lives of far too many people. Before investing, conduct thorough research, and only fund ventures in which you have a sincere belief.
- Buy a hardware wallet.
To further secure your portfolio, you can keep your assets on hardware wallets, called “cold storage,” which are safe hardware devices. Always carry out transactions using a hardware wallet, as doing so will shield you from most online threats. When looking for a hardware wallet that suits you the best, be sure to complete your research!
Here are a few of the most popular hardware wallets:
- Ledger Nano X
- Ledger Nano S
- Trezor Model One
- Steer clear of unidentified tokens
Never deal with unknown token airdrops that show up in your wallet. In a scam known as a “rug pull,” where the project’s developer vanishes with all the money, leaving you with worthless cryptocurrency, some con artists will employ this technique to persuade you to buy more.
Additionally, tokens can entice you to dubious websites you should always avoid because they will empty your wallet
- Protect your private information.
When your identity is at risk, then your cryptocurrency assets are too. A single leak or breach can lead to identity theft; therefore, protecting your personal information is essential.
The most effective approach to protect your personal information is to employ common sense: never, ever, ever share personal information with strangers or on social networking sites. In general, you want to avoid behaviours on open networks that can draw the attention of criminals.
Conclusion
For early investors, there are opportunities. Web3 offers more significant direct benefits to everyone than Web1 and Web2, whose primary beneficiaries were founders and venture capitalists. As a result, Web3 is a crucial instrument for achieving greater financial independence for all.
While trying to gain this financial independence, it is essential to take security seriously. You work hard to earn your money; therefore, you should work hard to keep it.
Try not to share too much information, do not connect your wallet to just about any decentralized app, do not click on any random links on any social media platform and be sure to stay safe.