Cryptography is a broad term that is in use more often daily. Yet, this concept is not particular to tech gurus, high-end security bodies, or personnel. Instead, cryptography applies to every modern technology user, including you.
At the end of this article, you should be able to understand the concept behind cryptography. You are to know the different types of cryptography and their differences. Finally, please familiarize yourself with the applications of cryptography and its function in blockchain technology.
Here is an outline of what we covered in this article:
- What is cryptography
- Types of cryptography
- A brief history of cryptography
- Types of cryptography
- How does cryptography work
- Types of cryptography algorithm
- Application of cryptography
- Use of cryptography in Blockchain
What Is Cryptography?
Since ancient times, writers protect handwritten letters from unauthorized parties using a technique known as encryption. Today, we also protect digital data through encryption. Encryption is a branch of computer science focusing on converting data into representations only authorized users can understand.
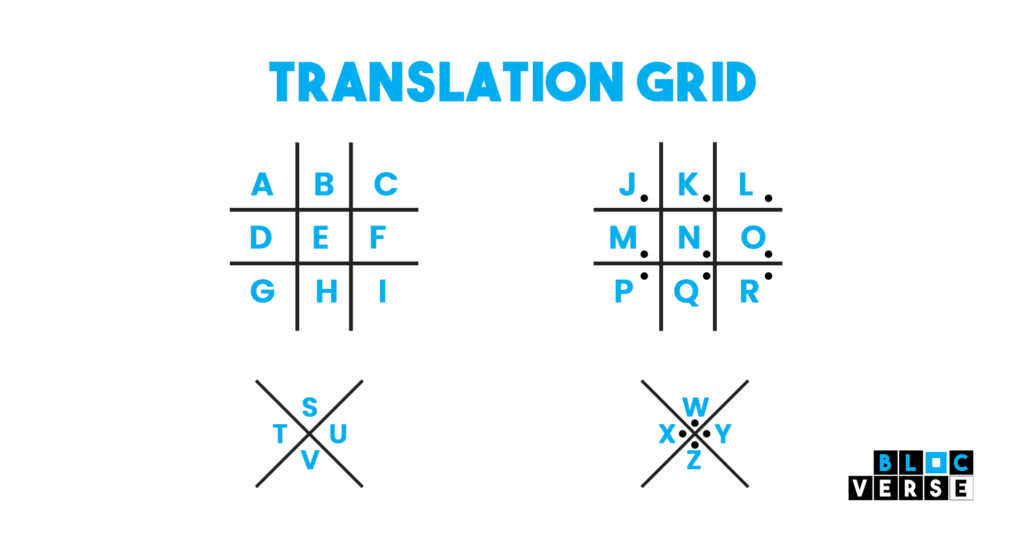
An example of fundamental cryptography is an encrypted message with letters substituted with other characters.
A grid or table outlining how to switch the letters around would be necessary to decode the encrypted text. For instance, one may translate using the translation grid below.
The Brief History Of Cryptography
It’s believed that writing and cryptography both developed at the same time. As civilizations developed, people began to organize themselves into tribes, clans, and kingdoms.
Because of this, people saw clarity in concepts like politics, supremacy, conflict, and power.
These theories stimulated people’s innate need to communicate with chosen recipients in a hush-hush manner. With this in mind, cryptography continued to advance.
Roman and Egyptian cultures are where cryptography first emerged.
Types Of Cryptography
There are three types of cryptography, and there are as follows:
- Symmetric key
- Asymmetric key
- Hash Function
Symmetric Key Cryptography
In a symmetric key, you can use “one key only,” sometimes called secret-key cryptography.
Using one key, both the sender and the recipient can encrypt and decrypt a communication.
A significant drawback of the symmetric key scheme is that the two parties must share the key. This is because both parties use one key for encryption and decryption. A case study is Blowfish – A symmetric key.
Asymmetric Key Cryptography
This type of cryptography is also known as “Public-key cryptography” as it uses two keys.
Compared to symmetric key, its encryption is safer and different. In this system, each user encrypts and decrypts data using two or a pair of keys (private and public keys).
The user can share their private key with the public across the network for communication. Because of this, the users protect their private keys to ensure safety.
You can encrypt the message using any of those keys and decrypt it using the final key. Asymmetric key uses methods like the RSA algorithm.
HASH Function
This algorithm doesn’t need any keys at all. Instead, the plain text generates a hash value with a set length. This method makes it hard to decipher the plain text. Several operating systems use hash functions to encrypt passwords.
How Does Cryptography Work?
Data exchanged between banks, credit card firms, clients, and other businesses uses cryptographic encryption. Cryptography protects this data during transmission and stores it in sizable databases.
Let’s use your credit card as a case study. Your card has encryption on its magnetic strip or integrated chip, allowing you to pay for your groceries when you swipe your credit card.
The payment processor receives the encrypted data and transmits it to a third party. They verify that you did not exceed your credit card limit before returning with an encrypted approval code.
The same operations occur when you use other payment methods, such as a debit card. Touchless NFC-based payment systems like Apple pay or Google pay apply similarly.
Data breaches would likely occur on a daily or, worse still, hourly basis without the usage of encryption, rather than the monthly occurrences they appear to be in the present day.
When a data breach makes the headlines, it is because there wasn’t enough encryption or too little encryption.
At this point, you should have understood that when you think cryptography, you should think of securities. The reason is that it allows safe communication when bad actors are present.
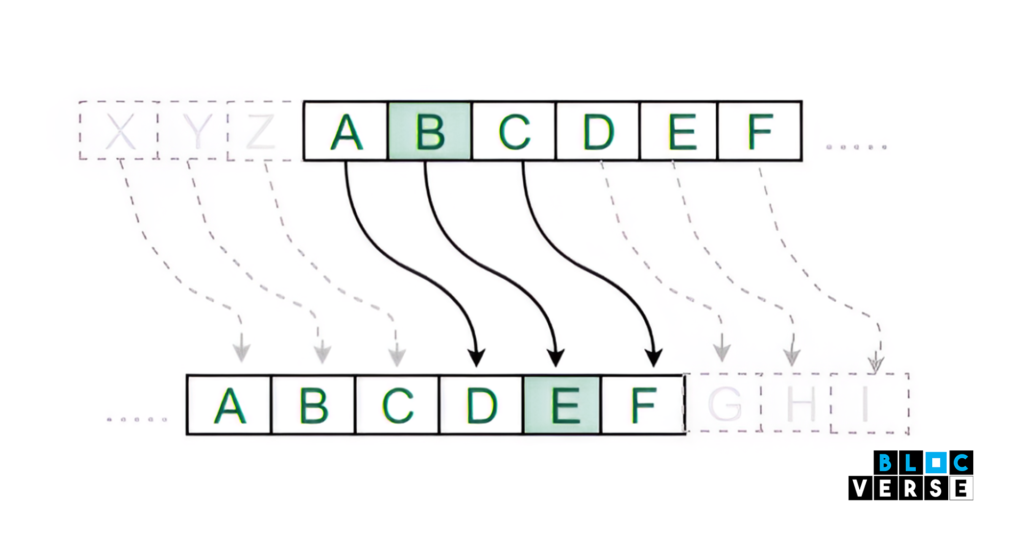
Encryption employs an algorithm and a key to convert an input known as plaintext(i.e., ordinary readable text) into an encrypted output (known as ciphertext (i.e., encrypted text. If we use the same key, an algorithm will always convert a given plaintext into a particular ciphertext.
A secure algorithm is one in which an attacker cannot infer details about the plaintext or key from the ciphertext. Given the vast majority of plaintext/ciphertext combinations that used a key, an attacker shouldn’t be able to find anything about it.
Types Of Cryptographic Algorithm
You can use cryptographic algorithms for essential tasks like authentication, data encryption, and digital signatures. There are two types of cryptographic algorithms.
Rivest-Shamir-Adleman (RSA) Algorithm:
The block cipher theory is the foundation for the asymmetric RSA cryptographic technique. At the receiving end, it transforms plaintext into ciphertext and vice versa. If you use User A’s public key for encryption, you must only use User A’s private key for decryption.
Data Encryption Standard:
This symmetric cipher algorithm uses the block cipher technique to encrypt and decrypt data. The algorithm creates ciphertext from plain text stored in 64-bit blocks using 48-bit keys. It uses the Fiesta Cipher Structure to function.
Application Of Cryptography
This method of security has a wide range of uses. These are a few of the applications:
Confidentiality: Cryptography enables the storage of encrypted data by users. This method eliminates the critical weakness of hacker circumvention.
Non-repudiation: The person who created the material or sent it cannot deny doing so.
Authentication: Assists in validating the sender, recipient, and information’s origin and destination.
Integrity: The inability to change information when storing or transporting it between the sender and intended recipient without noticing any addition to the data.
Use Of Cryptography In Blockchain
Blockchain developers used various cryptography concepts in the development of Blockchain. The result of cryptographic technology encourages restrictions on the ongoing development of Blockchain.
The Blockchain employs this method of security to maintain data consistency, safeguard user privacy, and preserve transaction information. It uses “digital signatures” in asymmetric cryptography for data integrity assurance.
For every transaction recorded to a block, the sender signs it using a digital signature, ensuring that the data is not corrupted.
Maintaining the integrity and security of the Blockchain is appropriate since secret writings is essential to keeping the public network secure.
Conclusion
Information is available in digital form in the modern world. Today, computer systems digitally record, process, and transfer important data.
Attackers aim at computers to get illegal access because the information is essential. In situations like this, encrypted messages help in providing adequate security.
While allowing authorized users to access data, secret writings provide a scalable set of measures that ensure the disruption of the attacker’s evil intentions.